As devices, homes, and cities become smarter, the interconnected network of devices known as the Internet of Things (IoT) will only grow in importance. The discussions surrounding IoT typically talk about its benefits, but it’s also important to note some potential risks associated with the technology.
Whether you’ve only heard the term IoT in passing or you’ve got a full suite of IoT hardware in your home, here’s what you need to keep in mind about the technology.
What Is IoT, and How Can It Benefit You?
By its basic definition, IoT refers to physical objects, machines, computers, and other smart devices that connect to the Internet. Other key aspects of IoT include being embedded with unique identifiers and having the ability to transfer data over a connection.
The “thing” portion of the term Internet of Things refers to those specific and individual devices. It can be a smartwatch or fitness tracker, a smart home thermostat, or a piece of city-owned technology used to monitor traffic. As long as it fits the prior definitions, it’s technically part of IoT.
As far as how this technology can be a boon to the everyday user, you’re probably already familiar with the benefits. Smart speakers allow you to easily control music playback and lighting with just the sound of your voice. A smart fitness tracker that connects to your smartphone can give you key insights into how much activity you’re getting. It is estimated that there will be 25.4 billion active IoT devices by 2030.
Some Risks of IoT Hardware
IoT hardware is dependent on the Internet, which means that a power outage or broken router could bring down a lot of the appliances and devices in your home. But, beyond that, there are two primary concerns when it comes to IoT devices: cybersecurity and privacy.
Privacy concerns
Even if your IoT hardware doesn’t get hacked, there are still some privacy considerations to take into account. Virtually every smart speaker on the market has, in the past, recorded users accidentally and without their knowledge.
Many IoT devices collect and transmit a lot of sensitive data, too. Just think back to all the fitness and health information that your wearable could be generating. If that information stays private, then it isn’t much of a concern. So it’s important to ask the tough questions about who has access to that data—whether it’s the manufacturer of your IoT hardware, your Internet service provider, or another third party.
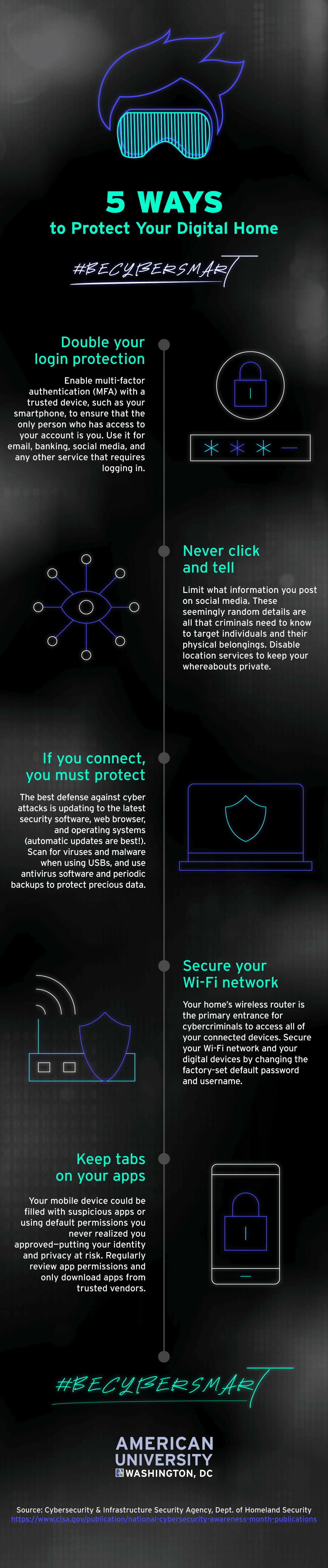
According to an IoT security tip sheet released during National Cybersecurity Awareness Month, it’s recommended that you check permissions for apps that control IoT hardware and learn to say “no” to privileges that you aren’t comfortable with.
Cybersecurity risks
Like other platforms, systems, and machines that connect to the Internet, IoT is vulnerable to external attacks from hackers and bad actors. Worse still, many IoT devices have less sophisticated security mechanisms than the average computer outfitted with a firewall and antivirus software.
There are other cybersecurity concerns surrounding IoT software, too. For example, a hacked security camera can pose serious privacy and physical security risk. And it only takes one story of a baby monitor being hacked to send chills down the spines of parents.
Luckily, there are some simple things you can do to mitigate the risk of compromise. The National Cybersecurity Awareness Month tip sheet recommends changing the default passwords on your IoT hardware. You may also want to consider placing IoT devices on a separate Wi-Fi network or band than the computers and hardware in your household.
If you’re ready to take your tech career further, the American University Cybersecurity Professional Program can help you gain the hands-on experience you need in less than one year. Learn what the day-to-day life of a cyber professional entails while receiving white-glove career services that will help you develop your personal brand. Throughout our 10-month program, you will connect with industry experts, gain real-world experience, and prepare for industry certifications that will allow you to stand out from other candidates.
Learn more about our cybersecurity program.




